Work Methodology
At Global Insights KPO, we understand that each client’s needs are unique, which is why we take a customized approach to every project. Our work methodology combines a strategic, step-by-step process with the flexibility to adapt to each client’s specific requirements. By integrating industry best practices, state-of-the-art tools, and effective communication, we ensure that all tasks are completed accurately and on time. Our approach helps us consistently deliver high-quality services that drive business efficiency and foster long-term partnerships.
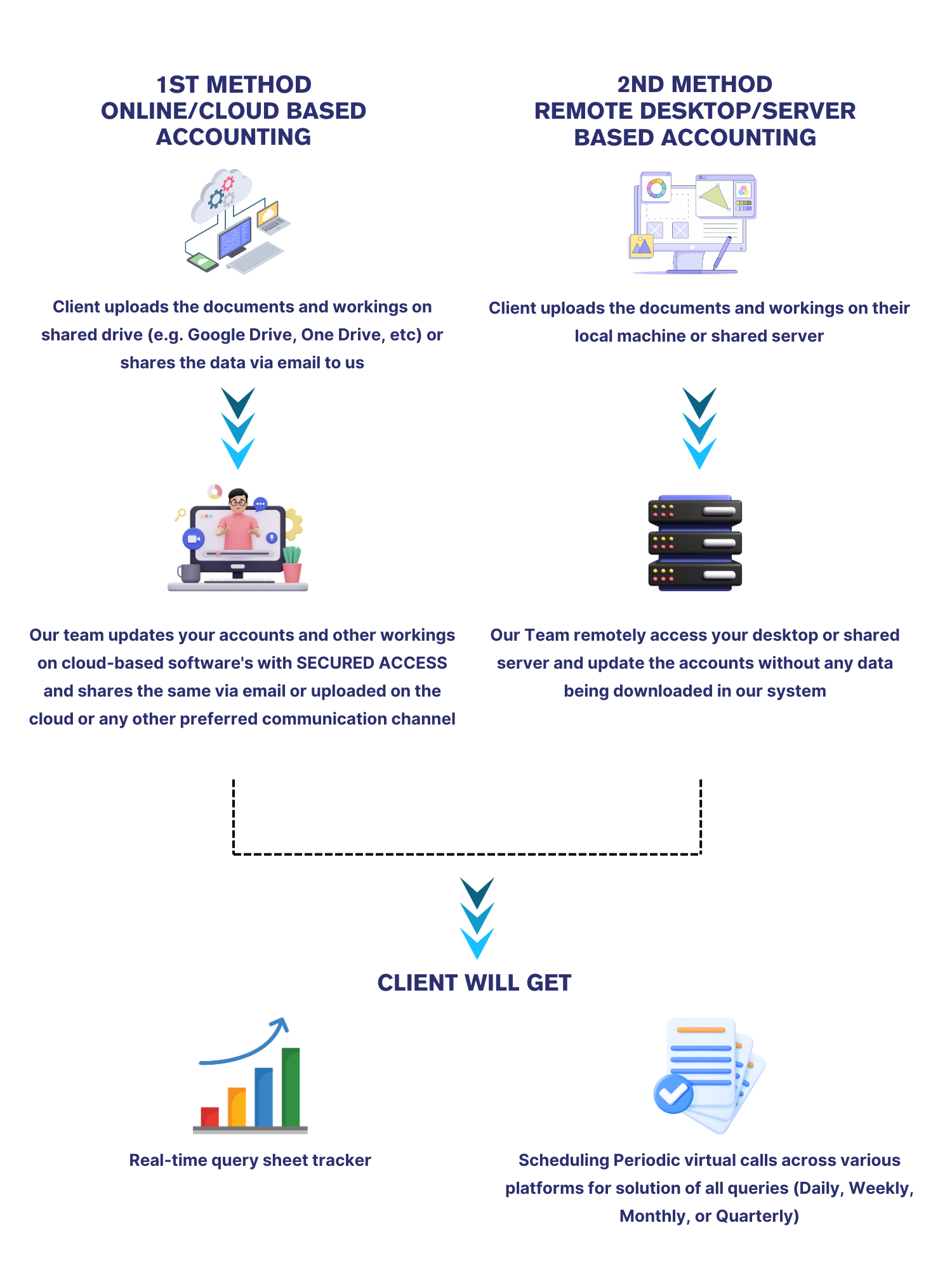
Our Workflow
Our 5-Step Work Methodology
At Global Insights KPO, we follow a structured and client-centric approach to ensure a seamless experience, high-quality service, and long-term value for our clients. Our 5-step work methodology ensures efficient onboarding, transparent communication, and continuous improvement.

1. Initial Consultation & Agreement
✓ Offer tailored services
✓ Provide cost-effective pricing.
✓ Sign SLA & start onboarding

2. Smooth Onboarding & Business Understanding
✓ Identify pain points & optimize workflow.
✓ Set up clear communication for support.

3. Secure Data & Software Access
✓ Ensure data confidentiality & security.
✓ Assign tasks per business needs.

4. Service Delivery & Reviews
✓ Conduct periodic review calls.
✓ Maintain transparency & collaboration.

5. Learning & Improvement
✓ Optimize processes for efficiency
✓ Gather & integrate client feedback.
Data Security
At Global Insights KPO, we prioritize financial data security, implementing robust protections against cyber threats, unauthorized access, and data breaches. Our multi-layered security approach ensures your information remains confidential and protected, giving you complete peace of mind. We go beyond industry standards to ensure your financial data remains safe, private, and secure—because your trust is our top priority.
End-to-End Protection
Advanced firewalls, endpoint security, and real-time threat detection block potential cyber risks.
Encrypted & Compliant
Data is fully encrypted and managed following industry best practices for privacy and security.
Web & Email Security
Protection against phishing, malicious websites, and email-based attacks to keep communications secure.
Strict Access Controls
Only authorized personnel can access data, with restrictions on unauthorized software or USB usage.
Data Loss Prevention (DLP)
Measures to prevent accidental leaks, unauthorized data transfers, or insider threats.
Anti-Ransomware & Threat Prevention
Multi-layered defenses safeguard your financial data from cyber threats.
On-Site Operations Only
All employees work on-site only, ensuring maximum security with no remote access.
Regular Security Audits & Updates
Continuous monitoring, security audits, and timely updates keep our systems secure.
Our Journey so far.....
Validated by our trusted clients. See our impact at a glance.
Industry Expertise
We blend industry insights with financial expertise to deliver unmatched accounting and back-office support. Our team prioritizes accuracy, compliance, and efficiency, enabling clients to focus on growth while we manage their financial operations.

Manufacturing

Franchising

Hospitality

Retail

Food & Beverages

Marketing Agencies

Real Estate

Information Technology
Accounting and Related Softwares












Communication Channels








Document Storing & Sharing Modes